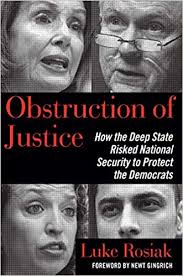
The following is an excerpt from 'Obstruction of Justice: How the Deep State Risked National Security to Protect the Democrats' by Luke Rosiak, just published by Regnery.
Somehow, a man named Imran Awan, his younger brothers Abid and Jamal, his friend Rao Abbas, and his wife Hina (Imran was a polygamist married to both Hina and Sumaira) were all on the congressional payroll as computer systems administrators. Each worked part-time for around eight members of Congress, forty-four in total. Their job was to configure servers, set up email accounts, and purchase phones and desktops for the offices. The problem is they were also logging onto the servers of other members of Congress who they didn’t work for. They were logging in using members of Congress’ personal usernames. They were funneling massive amounts of data off the network. They were accessing the House Democratic Caucus server with a bizarre frequency—five thousand times within a few months. And they used elaborate digital techniques to conceal what they were doing.
Representative Michelle Lujan Grisham of New Mexico had terminated Abid in 2015, before these other problems became known, but he kept logging into her servers after he was fired. In early 2015, Representative Kyrsten Sinema of Arizona had fired the youngest of the three Awan brothers, Jamal, for “incompetence.” He was a well-paid incompetent, joining the congressional payroll at $165,000 when he was only twenty years old and was still employed by many of her colleagues. And why had the Awans’ elderly father Muhammad, a religious cleric who spent much of his time in Pakistan and who had not a lick of IT skills, been briefly on the congressional payroll as the systems administrator for then Congressman, now-Senator, Joe Donnelly of Indiana?
It was July 25, 2016, three days after WikiLeaks threw a bomb into the presidential race and permanently brought politics’ dirty tricks into the modern age by publishing the first of the DNC’s emails, when Theresa brought the first results of her months-long cybersecurity probe to the body that oversaw her work, the Committee on House Administration. The timing of the discovery of the server logs documenting their behavior made the seriousness of it all impossible to miss. WikiLeaks was publishing the DNC’s emails on a weekly schedule, reminding politicians that cybersecurity breaches were a real and omnipresent threat. The threat of malicious actors inside the highest levels of the government itself should have made the infiltration of the DNC, a private fundraising group, pale in comparison assuming Democrats valued data from their country’s government above that of their party.
Republican Congresswoman of Michigan chaired the committee, but in practice, congressional staff runs much of Congress, especially sleepy minor committees like this one. Theresa reported her findings to the committee’s Republican staff director, Sean Moran.
Sean is a mild-mannered veteran congressional staffer with a short, slight frame and one of the rare gray-haired heads in a complex dominated by youngsters. He found the specifics hard to follow. After all, he only had two apps on his iPhone and it took his wife to install them. When he echoed his understanding of the findings to people later, it showed, saying “terabits” where he meant “terabytes,” and saying the Awans used “codes” rather than “scripts.” But the significance wasn’t lost on him. It was obvious that the committee needed to bring this to the top—Speaker Paul Ryan and Minority Leader Nancy Pelosi—and fast.
Speaker Ryan’s office told Theresa to continue her investigation, but there was a complication. While many IT aides worked for members of both parties, the Awans worked exclusively for Democrats, so the investigation had to be done in a way acceptable to Democrats. A meeting was set up in the office of Kelly Craven, Ryan’s chief for internal affairs, about how to get to the bottom of it. The answer was very slowly or not at all. Craven heard viewpoints offered on one side by Nancy Pelosi’s counsel, Bernie Raimo, and on the other, Paul Ryan’s general counsel, Mark Epley.
Raimo said, “These are our employees. You can’t look at any files or interview them without getting permission from their bosses first.”
Theresa protested, “That’s forty-four members!”.
“Oh, and you can’t ask any members because that will disclose the case,” Raimo added.
When Theresa complained that it was impossible to conduct an investigation under those restrictions, Raimo yelled, “You’re not the policeman of the world!”
That meant Theresa was tasked with doing a cybersecurity investigation in which she was banned from talking to the suspects or their employers and had to watch data fly off the network without knowing what it was. Theresa considered where that left her. The Awans’ fraudulent billing of congressional offices for computers and other equipment wasn’t as critical as the cybersecurity breaches, but the falsified receipts contained easily provable lies. Those lies might enable police to put the Awans behind bars before they dismantled more evidence and did more harm. She just needed to learn how the falsified receipts were generated. She could at least search the Awans’ government email accounts, right?
Raimo said no. The initial complaints named only Abid, so including the other family members would amount to a “fishing expedition.” On top of that, Raimo cited the “speech and debate clause” of the Constitution. That clause states that members of Congress “shall in all Cases, except Treason, Felony and Breach of the Peace, be privileged from Arrest during their attendance at the Session of their Respective Houses, and in going to and from the same; and for any Speech or Debate in either House, they shall not be questioned in any other Place.” The clause is part of the Constitution’s separation of powers and is intended to protect members of Congress from the executive branch. Raimo argued that it extended to IT support staff like the Awans, and implied that it protected them from Theresa’s investigation even though she was part of the legislative branch.
Theresa offered a concession: have a third party use a computer command to pull only those emails sent to or about the federal contractor CDW-G. Authorities could then learn whether the Awans were running a fraud scheme, CDW-G was responsible, or the Awans had a man inside CDW-G. Whatever they found would be significant because CDW-G was a multi-billion dollar company that did business throughout the federal government. This was classic government accountability work.
Even that was too much for Pelosi’s man. Craven looked at Ryan’s general counsel, Mark Epley, a former aide to the Deputy Attorney General at the Department of Justice, to settle the dispute. He wasn’t making much of an effort to push back. Internal matters were different than the hard-fought legislative battles that played out along party lines each day on the campus. Such issues inside the House were more personal and routinely defined by bipartisan agreement, with a lack of consensus defaulting to inaction. Epley offered a meager, but classically bureaucratic, compromise: the House would preserve the Awans’ emails, but for now, no one would look at them. When the meeting adjourned, no such bargain was reached for accessing data that held the key to what by all appearances were major cybersecurity violations.
Paul Ryan wasn’t just the head of House Republicans, he was the leader of an institution with hundreds of years of precedent and a reputation to preserve. The Democrats were in the minority, but they were far more invested in shaping this case than the Republicans, who didn’t seem to know much about it.
For all Craven, Epley, and Raimo knew, the Awans might have been working for a foreign intelligence service, selling sensitive information to the highest bidder, or dealing in extortion or blackmail. Neither party in Congress seemed interested in finding out, at least not before the 2016 elections. Politics took precedence.